Website owners keenly depended on WordPress plugins. And they install whatever they need to make the website beautiful and their workload bearable. The problem arises when they can not check the vulnerabilities of a plugin, and it affects the website badly. Like- deleting files, and injecting spammy links into the content. The worst is stealing sensitive information like passwords and credit card numbers.
You must know how to check plugin vulnerabilities in WordPress to keep your website secure and trustworthy.
We will show you the most effective and reliable way to detect malware plugins and kick them out.
What are Malware Plugins?
Plugin-related vulnerabilities in WordPress refer to third-party plugins’ design, implementation, or functionality flaws. Through this, attackers could exploit a WordPress website to gain unauthorized access or compromise the website’s security.
These vulnerabilities can take various forms, such as Cross-Site Scripting (XSS), SQL injection, Remote Code Execution (RCE), Cross-Site Request Forgery (CSRF), and many others.
The consequences of plugin-related vulnerabilities can be severe, including website defacement, data theft, website downtime, and reputational damage.
Therefore, it is essential to regularly monitor and update plugins on a WordPress site to mitigate the risk of plugin-related vulnerabilities. The most secure and easy way to make it happen is using the third-party premium plugin.
How to Check Plugin Vulnerabilities in WordPress?
It’s almost impossible for site owners to figure out the vulnerability of any plugin. Let’s see how you can do this within a few clicks.
Step 1: Install Eazy Plugin Manager
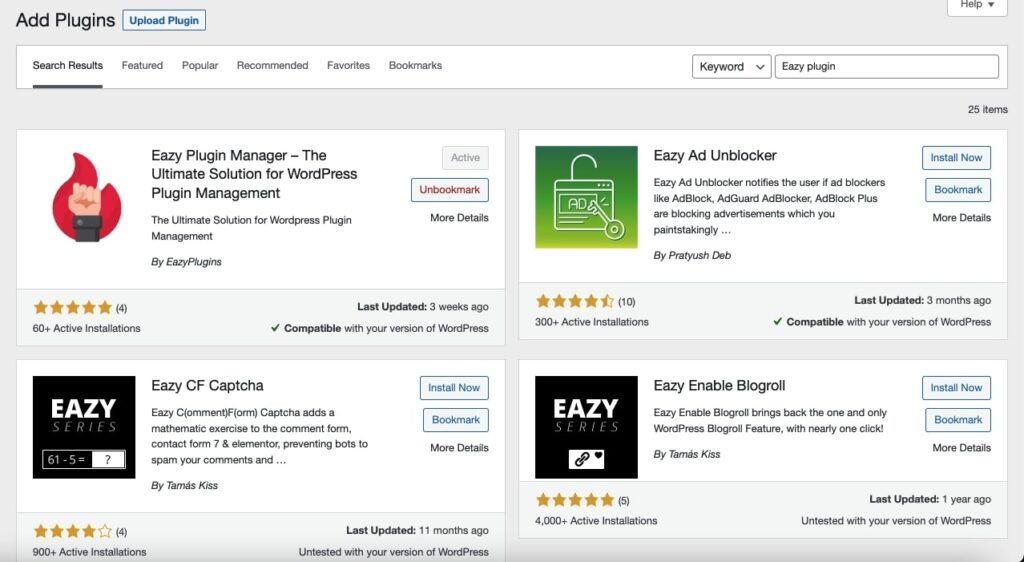
Install and activate Eazy Plugin Manager in your WP admin dashboard. You must purchase the Pro version; otherwise, you cannot use it.
Step 2: Detect notification about plugin-related vulnerability
You can see a red bubble in the sidebar beside the Active Guard option if Eazy Plugin Manager detects any threat.
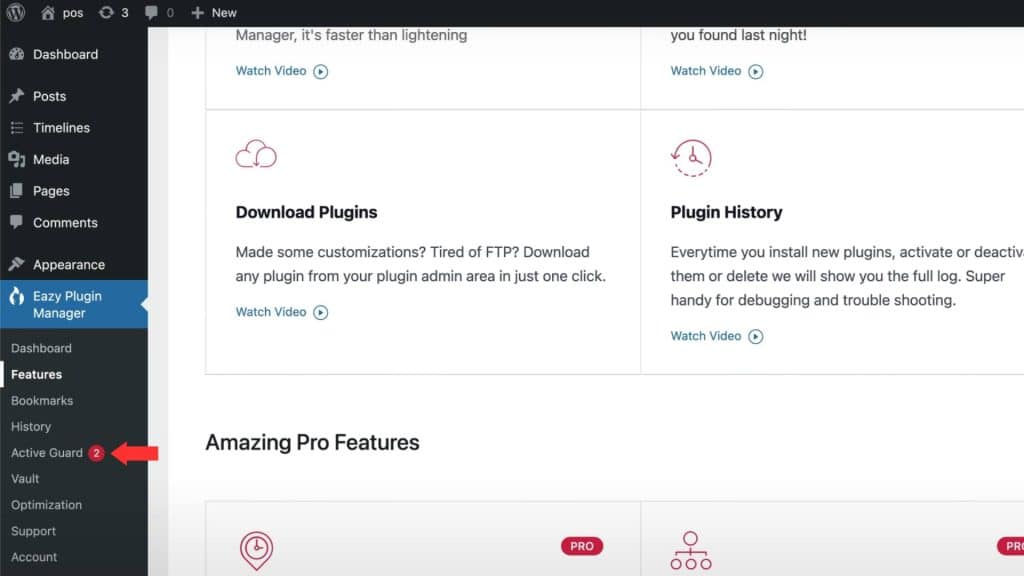
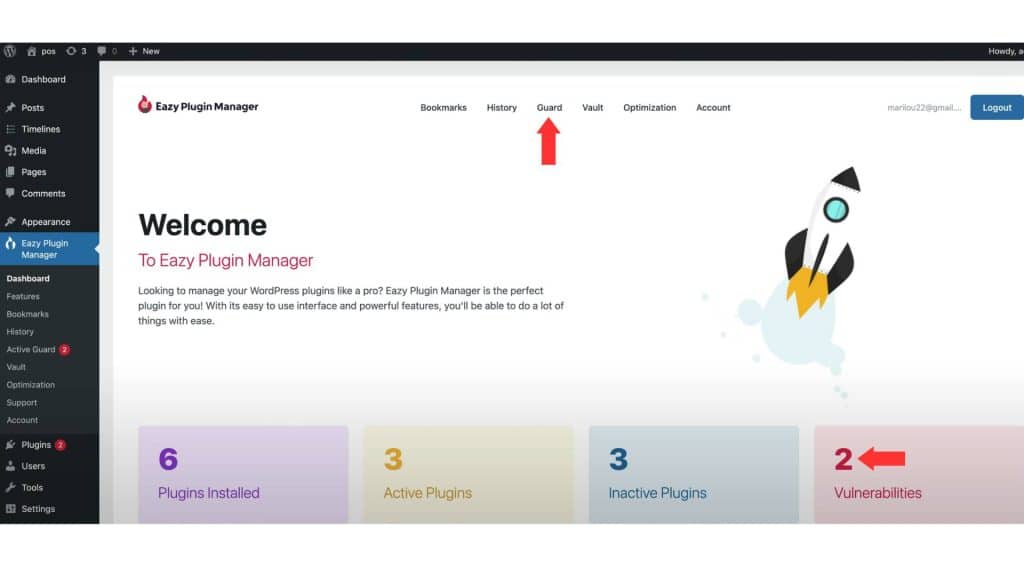
Head over to the Dashboard of EPM for detailed information about the issue. On the landing page of Eazy Plugin Manager, you can see the number of Vulnerabilities.
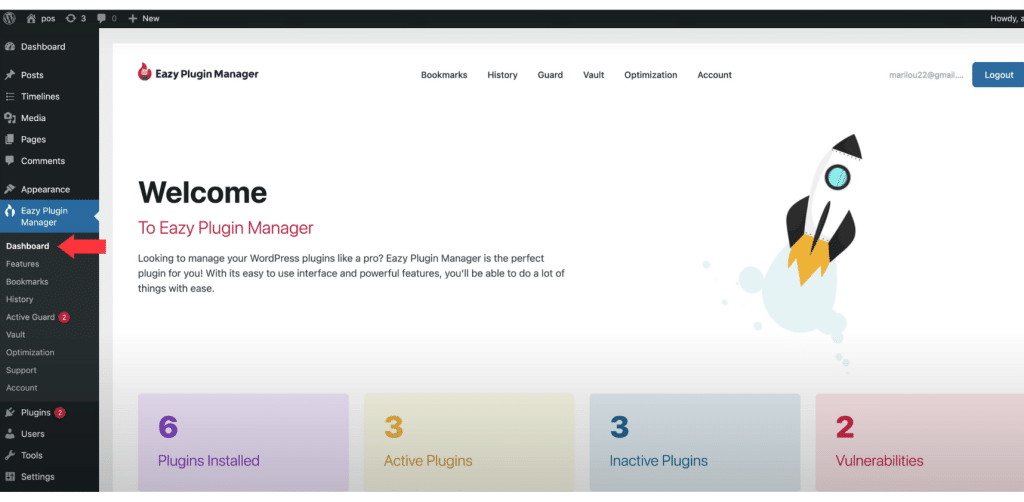
Now click on the Guard option from the top bar to take necessary action about the infected plugins.
Step 3: Get detailed data about plugin-related threat
The new page will show every detail of those security issues. You will see the plugin’s name, the current version you are using, and the severity level of the threat. Other than that, you will get a short description of the problem.
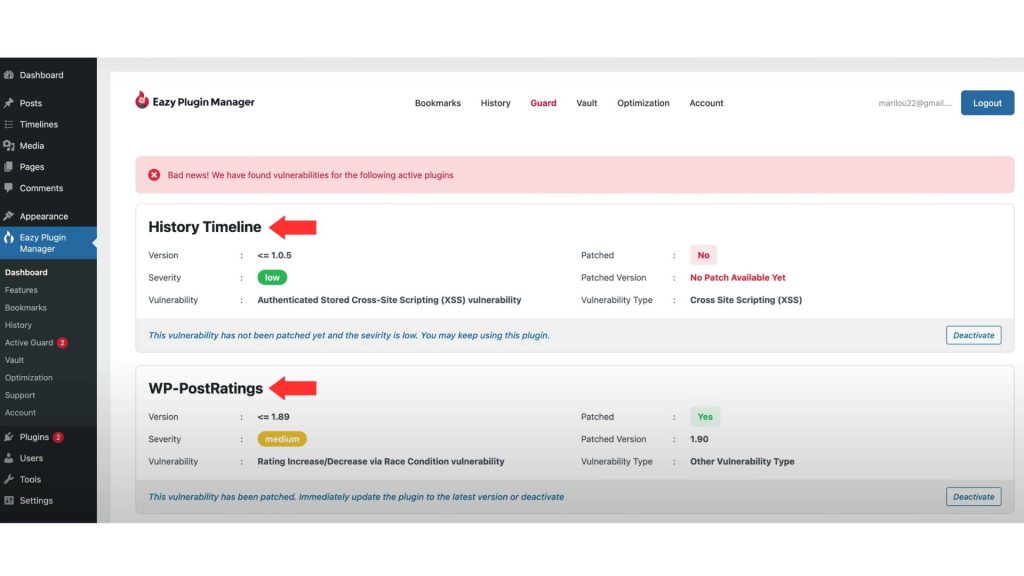
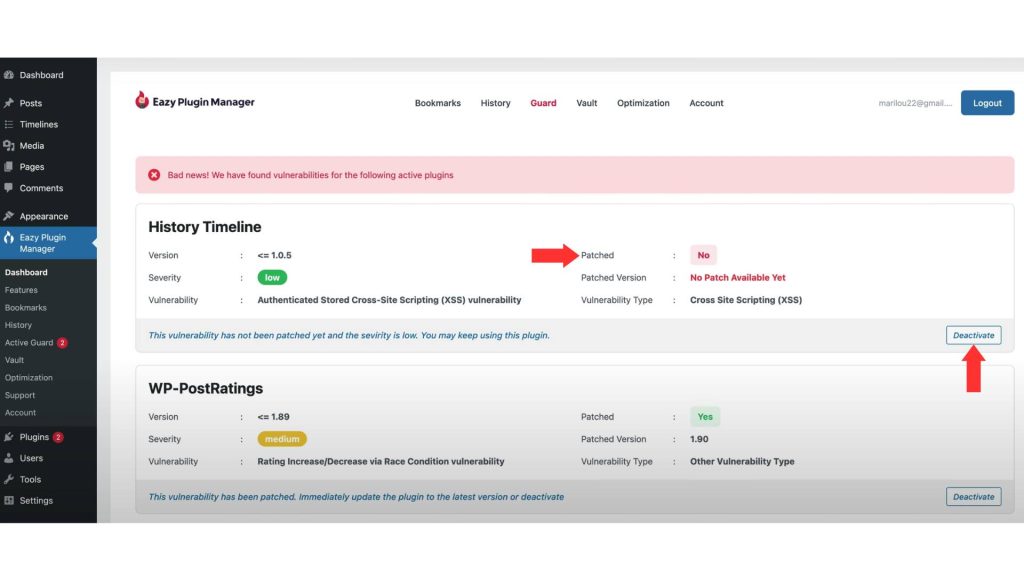
Eazy Plugin Manager not only detects the vulnerability but also suggests solutions. If a patch is available, it will offer the new patch version number of the plugin. If no patch is released, then EPM will suggest you deactivate the plugin for that time.
A dedicated deactivated button will be found for each vulnerable plugin. Hit that Deactivate button and protect your WordPress site from any possible mishaps.
The Dominant Active Guard Feature
The feature you just experienced in this blog is known as Active Guard. This is a premium security feature that keeps your website safe. EPM updates its vulnerability database regularly and notifies you of any issues about your installed plugins.
Active Guard also provides solutions based on the severity level of the threat. You can stay secure with EPM’s advanced protection and have peace of mind knowing your site is protected from malware.
FAQ (s)
What are plugin vulnerabilities in WordPress?
Plugin vulnerabilities refer to security issues in WordPress plugins that attackers could exploit to gain unauthorized access to a website. Also, they can perform other malicious activities.
How can I check if my WordPress plugins have vulnerabilities?
There are several ways to check for plugin vulnerabilities in WordPress. One way is to use a plugin vulnerability scanner, such as WPScan or Plugin Vulnerabilities. You can also check the vulnerability database of the WordPress.org plugin repository.
What information can I get from a plugin vulnerability scan?
A plugin vulnerability scan can provide information on any known vulnerabilities in the plugins installed on your WordPress site. The should include the severity of the vulnerability, the version of the plugin that is affected, and any available patches or updates.
How often should I check for plugin vulnerabilities?
It’s a good practice to check for plugin vulnerabilities regularly, ideally weekly or monthly. This can help you to identify and address any security issues before attackers exploit them.
What should I do if I find a plugin vulnerability on my WordPress site?
If you find a plugin vulnerability on your WordPress site, immediately address it. This may involve updating the affected plugin to the latest version. Remove it if it is no longer supported or has not been updated, or implement other security measures, such as adding a firewall or security plugin.
How can I prevent plugin vulnerabilities in WordPress?
To prevent plugin vulnerabilities in WordPress, it’s essential to keep all plugins up to date and remove any plugins that are no longer in use. Other options are-
- Limit the number of plugins installed on your site
- Use reputable plugins from trusted sources
- Implement other security measures, such as adding a firewall or using a security plugin.
Final Saying
Checking plugin vulnerabilities in WordPress is a critical step toward maintaining the security and integrity of your website.
With the ever-increasing number of WordPress plugins, it’s essential to regularly check for vulnerabilities and keep them updated to ensure that your website is protected against potential security threats.
Now it’s your time to decide whether you will do it by yourself or assign EPM for it.
